Attack surfaces are growing faster than security teams can keep up. To stay ahead, you need to know what’s exposed and where attackers are most likely to strike. With cloud migration dramatically increasing the number of internal and external targets, prioritizing threats and managing your attack surface from an attacker’s perspective has never been more important. Let’s look at why it’s growing, and how to monitor and manage it properly with tools like Intruder.
What is your attack surface?
First, it’s important to understand that your attack surface is the sum of your digital assets that are ‘exposed’ – whether the digital assets are secure or vulnerable, known or unknown, in active use or not. This attack surface changes continuously over time, and includes digital assets that are on-premises, in the cloud, in subsidiary networks, and in third-party environments. In short, it’s anything that a hacker can attack.
What is attack surface management?
Attack surface management is the process of discovering these assets and services and then reducing or minimizing their exposure to prevent hackers exploiting them. Exposure can mean two things: current vulnerabilities such as missing patches or misconfigurations that reduce the security of the services or assets. But it can also mean exposure to future vulnerabilities.
Take the example of an admin interface like cPanel or a firewall administration page – these may be secure against all known current attacks today, but a vulnerability could be discovered in the software tomorrow – when it immediately becomes a significant risk. An asset doesn’t need to be vulnerable today to be vulnerable tomorrow. If you reduce your attack surface, regardless of vulnerabilities, you become harder to attack tomorrow.
So, a significant part of attack surface management is reducing exposure to possible future vulnerabilities by removing unnecessary services and assets from the internet. This what led to the Deloitte breach and what distinguishes it from traditional vulnerability management. But to do this, first you need to know what’s there.
Asset management vs vulnerability management
Often considered the poor relation of vulnerability management, asset management has traditionally been a labour intensive, time-consuming task for IT teams. Even when they had control of the hardware assets within their organization and network perimeter, it was still fraught with problems. If just one asset was missed from the asset inventory, it could evade the entire vulnerability management process and, depending on the sensitivity of the asset, could have far reaching implications for the business.
Today, it’s a whole lot more complicated. Businesses are migrating to SaaS and moving their systems and services to the cloud, internal teams are downloading their own workflow, project management and collaboration tools, and individual users expect to customize their environments. When companies expand through mergers and acquisitions too, they often take over systems they’re not even aware of – a classic example is when telco TalkTalk was breached in 2015 and up to 4 million unencrypted records were stolen from a system they didn’t even know existed.
Shifting security from IT to DevOps
Today’s cloud platforms enable development teams to move and scale quickly when needed. But this puts a lot of the responsibility for security into the hands of the development teams – shifting away from traditional, centralized IT teams with robust, trusted change control processes.
This means cyber security teams struggle to see what is going on or discover where their assets are. Similarly, it’s increasingly hard for large enterprises or businesses with dispersed teams – often located around the world – to keep track of where all their systems are.
As a result, organizations increasingly understand that their vulnerability management processes should be baked into a more holistic ‘attack surface management’ process because you must first know what you have exposed to the internet before you think about what vulnerabilities you have, and what fixes to prioritize.
Essential features of attack surface management tools
Various tools on the market are good for asset discovery, finding new domains which look like yours and spotting websites with similar content to your own. Your team can then check if this is a company asset or not, choose whether it’s included in your vulnerability management processes, and how it is secured. But this requires an internal resource because the tool can’t do this for you.
Similarly, some tools focus only on the external attack surface. But since a common attack vector is through employee workstations, attack surface management should include internal systems too. Here are three essential features that every attack surface monitoring tool should provide:
1. Asset discovery
You can’t manage an asset if you don’t know it exists. As we’ve seen, most organizations have a variety of “unknown unknowns,” such as assets housed on partner or third-party sites, workloads running in public cloud environments, IoT devices, abandoned IP addresses and credentials, and more. Intruder’s CloudBot runs hourly checks for new IP addresses or hostnames in connected AWS, Google Cloud or Azure accounts.
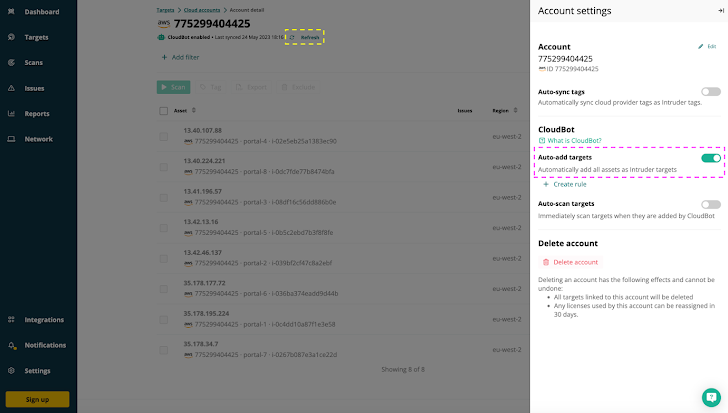 |
| Intruder’s CloudBot automatically adds any new external IP addresses or hostnames in cloud accounts as targets for monitoring & vulnerability scanning. |
2. Business context
Not all attack vectors are created equal and the ‘context’ – what’s exposed to the internet – is a vital part of attack surface management. Legacy tools don’t provide this context; they treat all attack surfaces (external, internal office, internal datacentre) the same, and so it’s hard to prioritize vulnerabilities. Attack surface management tools identify the gaps in your internal and external security controls to reveal the weaknesses in your security that need to be addressed and remediated first.
Intruder takes this a step further and provides insight into any given asset, and the business unit the application belongs to. As an example, knowing whether a compromised workload is a part of critical application managing bank-to-bank SWIFT transactions will help you formulate your remediation plan.
3. Proactive and reactive scans
You can’t just test your attack surface once. Every day it continues to grow as you add new devices, workloads, and services. As it grows the security risk grows too. Not just the risk of new vulnerabilities, but also misconfigurations, data exposures or other security gaps. It’s important to test for all possible attack vectors, and it’s important to do it continuously to prevent your understanding from becoming outdated.
Even better than continuous scanning is a platform that can scan proactively or reactively depending on the circumstances. For example, reacting to a new cloud service being brought online by launching a scan, or proactively scanning all assets as soon as new vulnerability checks become available.
Reducing your attack surface with Intruder
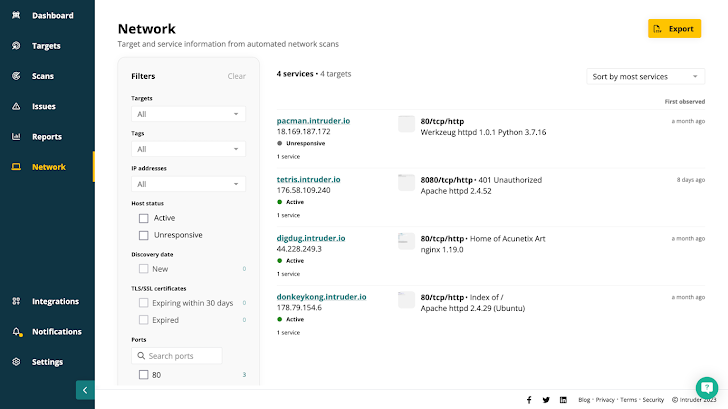
Attack surface monitoring tools like Intruder do all this and more. Intruder makes sure that everything you have facing the internet is supposed to be – by making it easily searchable and explorable. Its Network View feature shows exactly what ports and services are available, including screenshots of those that have websites or apps running on them.
Most automated tools are great at spitting out data for analysts to look at, but not at reducing the ‘noise’. Intruder prioritizes issues and vulnerabilities based on context, or whether they should be on the internet at all. Combined with Intruder’s continuous monitoring and emerging threat scans, this makes it much easier and quicker to find and fix new vulnerabilities before they can be exploited.
Try Intruder for yourself!
With its attack surface monitoring capabilities, Intruder is solving one of the most fundamental problems in cybersecurity: the need to understand how attackers see your organization, where they are likely to break in, and how you can identify, prioritize and eliminate risk.Ready to get started ?