The recent attack against Microsoft’s email infrastructure by a Chinese nation-state actor referred to as Storm-0558 is said to have a broader scope than previously thought.
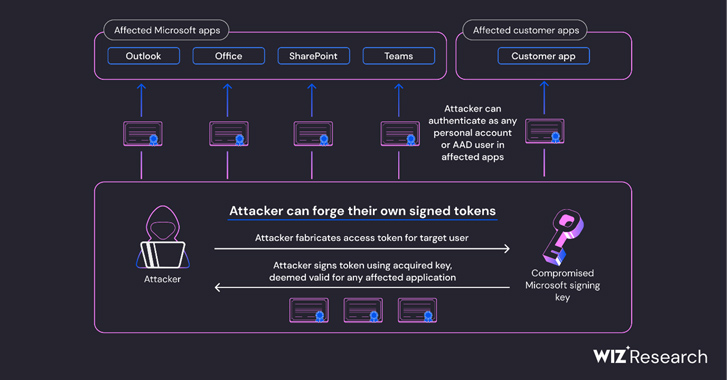
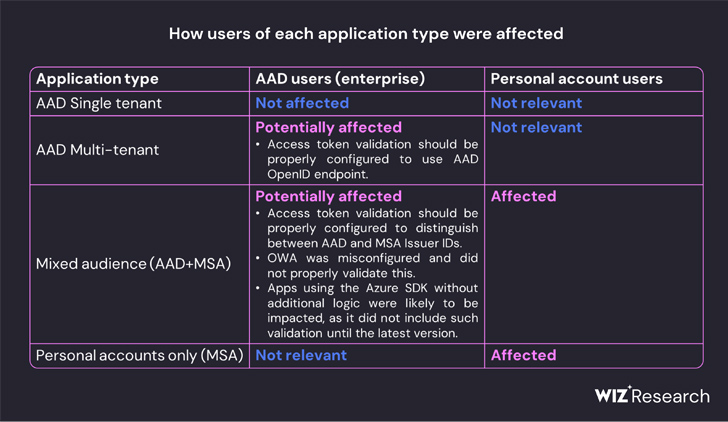
According to cloud security company Wiz, the inactive Microsoft account (MSA) consumer signing key used to forge Azure Active Directory (Azure AD or AAD) tokens to gain illicit access to Outlook Web Access (OWA) and Outlook.com could also have allowed the adversary to forge access tokens for various types of Azure AD applications.
This includes every application that supports personal account authentication, such as OneDrive, SharePoint, and Teams; customers applications that support the “Login with Microsoft functionality,” and multi-tenant applications in certain conditions.
“Everything in the world of Microsoft leverages Azure Active Directory auth tokens for access,” Ami Luttwak, chief technology officer and co-founder of Wiz, said in a statement. “An attacker with an AAD signing key is the most powerful attacker you can imagine, because they can access almost any app – as any user. This is a ‘shape shifter’ superpower.”
Microsoft, last week, disclosed the token forging technique was exploited by Storm-0558 to extract unclassified data from victim mailboxes, but the exact contours of the cyber espionage campaign remains unknown.
The Windows maker said it’s still investigating as to how the adversary managed to acquire the MSA consumer signing key. But it’s unclear if the key functioned as a master key of sorts to unlock access to data belonging to nearly two dozen organizations.
Wiz’s analysis fills in some of the blanks, with the company discovering that “all Azure personal account v2.0 applications depend on a list of 8 public keys, and all Azure multi-tenant v2.0 applications with Microsoft account enabled depend on a list of 7 public keys.”
It further found that Microsoft replaced one of the the listed public keys (thumbprint: “d4b4cccda9228624656bff33d8110955779632aa”) that had been present since at least 2016 sometime between June 27, 2023, and July 5, 2023, around the same period the company said it had revoked the MSA key.
“This led us to believe that although the compromised key acquired by Storm-0558 was a private key designed for Microsoft’s MSA tenant in Azure, it was also able to sign OpenID v2.0 tokens for multiple types of Azure Active Directory applications,” Wiz said.
Shield Against Insider Threats: Master SaaS Security Posture Management
Worried about insider threats? We’ve got you covered! Join this webinar to explore practical strategies and the secrets of proactive security with SaaS Security Posture Management.
“Storm-0558 seemingly managed to obtain access to one of several keys that were intended for signing and verifying AAD access tokens. The compromised key was trusted to sign any OpenID v2.0 access token for personal accounts and mixed-audience (multi-tenant or personal account) AAD applications.”
This effectively meant that the loophole could theoretically enable malicious actors to forge access tokens for consumption by any application that depends on the Azure identity platform.
Even worse, the acquired private key could have been weaponized to forge tokens to authenticate as any user to an affected application that trusts Microsoft OpenID v2.0 mixed audience and personal-accounts certificates.
“Identity provider’s signing keys are probably the most powerful secrets in the modern world,” Wiz security researcher Shir Tamari said. “With identity provider keys, one can gain immediate single hop access to everything, any email box, file service, or cloud account.”
Update
When reached for comment, Microsoft shared the following statement with The Hacker News –
Many of the claims made in this blog are speculative and not evidence-based. We recommend that customers review our blogs, specifically our Microsoft Threat Intelligence blog, to learn more about this incident and investigate their own environments using the Indicators of Compromise (IOCs) that we’ve made public. We’ve also recently expanded security logging availability, making it free for more customers by default, to help enterprises manage an increasingly complex threat landscape.