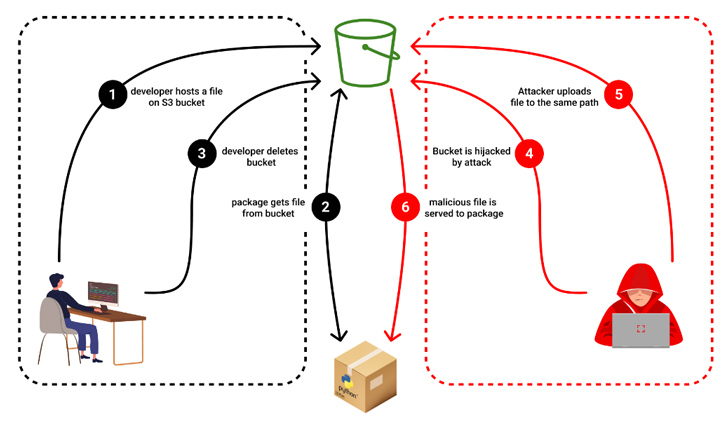
In what’s a new kind of software supply chain attack aimed at open source projects, it has emerged that threat actors could seize control of expired Amazon S3 buckets to serve rogue binaries without altering the modules themselves.
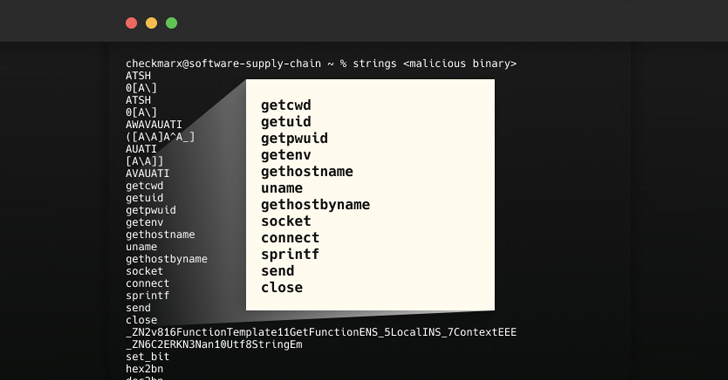
“Malicious binaries steal the user IDs, passwords, local machine environment variables, and local host name, and then exfiltrates the stolen data to the hijacked bucket,” Checkmarx researcher Guy Nachshon said.
The attack was first observed in the case of an npm package called bignum, which, until version 0.13.0, relied on an Amazon S3 bucket to download pre-built binary versions of an addon named node-pre-gyp during installation.
“These binaries were published on a now-expired S3 bucket which has since been claimed by a malicious third party which is now serving binaries containing malware that exfiltrates data from the user’s computer,” according to a GitHub advisory published on May 24, 2023.
An unknown threat actor is said to have seized on the opportunity that the S3 bucket was once active to deliver malware when unsuspecting users downloaded the package in question.
“If a package pointed to a bucket as its source, the pointer would continue to exist even after the bucket’s deletion,” Nachshon explained. “This abnormality allowed the attacker to reroute the pointer toward the taken-over bucket.”
A reverse engineering of the malware sample has revealed that it’s capable of plundering user credentials and environment details, and transmitting the information to the same hijacked bucket.
Checkmarx said it found numerous packages using abandoned S3 buckets, making them susceptible to the novel attack vector. If anything, the development is a sign that threat actors are constantly on the lookout for different ways to poison the software supply chain.
🔐 Mastering API Security: Understanding Your True Attack Surface
Discover the untapped vulnerabilities in your API ecosystem and take proactive steps towards ironclad security. Join our insightful webinar!
“This new twist in the realm of subdomain takeovers serves as a wake-up call to developers and organizations,” Nachshon said. “An abandoned hosting bucket or an obsolete subdomain is not just a forgotten artifact; in the wrong hands, it can become a potent weapon for data theft and intrusion.”
The development also comes nearly a week after Cyble unearthed 160 malicious python packages that are estimated to have been downloaded over 45,000 times and featured capabilities to extract login credentials and credit card details.